Is Online Voting Secure? How Providers Protect Your Vote
Thursday, 9 April 2026, 7:31 am

Is Online Voting Secure? How Providers Protect Your Vote
Security is the number one concern when it comes to online voting—and rightly so. Whether used for corporate resolutions, union ballots, or member votes, the integrity of the process must be beyond question. In Australia, regulatory expectations and best practices set a high bar for privacy, transparency, and fraud prevention.
This guide explains how reputable online voting providers protect your vote, drawing on current Australian government guidance and globally recognised security standards.
Is Online Voting Secure?
Yes—online voting can be highly secure when delivered by a reputable provider using modern security architecture, strict governance controls, and independent verification.
The Australian Cyber Security Centre (ACSC) emphasises that strong encryption, identity controls, and system monitoring are essential for protecting sensitive data and digital transactions.
https://www.cyber.gov.au/acsc/view-all-content/publications/essential-eight-maturity-model
Similarly, the Office of the Australian Information Commissioner (OAIC) highlights the importance of protecting personal information through robust security safeguards under the Privacy Act 1988.
https://www.oaic.gov.au/privacy/australian-privacy-principles-guidelines
When these principles are applied correctly, online voting systems can meet—and often exceed—the security of traditional paper-based methods.
Is Online Voting Secure in Australia?
In Australia, online voting must align with:
For example, the Australian Securities and Investments Commission (ASIC) outlines requirements for conducting member votes and maintaining accurate records.
https://asic.gov.au/regulatory-resources/find-a-document/regulatory-guides/
When implemented correctly, online voting platforms can comply with these obligations while improving accessibility, participation, and auditability.
Encryption: How Votes Are Protected in Transit and Storage
A cornerstone of secure online voting is end-to-end encryption (E2EE).
This means:
Encryption protocols such as TLS (Transport Layer Security) ensure that data cannot be intercepted or altered.
The ACSC strongly recommends encryption as a baseline control for protecting sensitive data.
https://www.cyber.gov.au/acsc/view-all-content/guidance-materials/encryption
For voters, this means your vote is protected from interception at every stage of the process.
Voter Authentication: Preventing Unauthorised Access
Secure voting providers implement strict authentication measures to ensure only eligible voters can participate.
Common protections include:
The ACSC recommends multi-factor authentication as one of the most effective ways to prevent unauthorised access.
https://www.cyber.gov.au/acsc/view-all-content/publications/multi-factor-authentication
These controls significantly reduce the risk of impersonation or duplicate voting.
Anonymity: Separating Identity from the Vote
A key requirement in many voting contexts is ballot secrecy.
Secure systems achieve this by:
This aligns with the Australian Privacy Principles, which require organisations to minimise the collection and exposure of personal data.
In practice, this ensures that while eligibility is verified, the content of your vote remains private.
Audit Trails: Transparency and Independent Verification
Reputable online voting platforms provide comprehensive audit trails, including:
These audit mechanisms ensure that:
The Australian National Audit Office (ANAO) highlights the importance of auditability and transparency in public sector processes.
https://www.anao.gov.au/work/performance-audit
This level of traceability is often more robust than traditional paper-based voting.
Certifications and Testing: Proving Security Standards
Trusted providers demonstrate their commitment to security through recognised certifications and ongoing testing.
Key indicators include:
The Australian Government recognises ISO 27001 as a benchmark for managing information security risks.
https://www.cyber.gov.au/acsc/view-all-content/publications/ism
What to Look for When Evaluating an Online Voting Provider
When selecting a provider, organisations should assess:
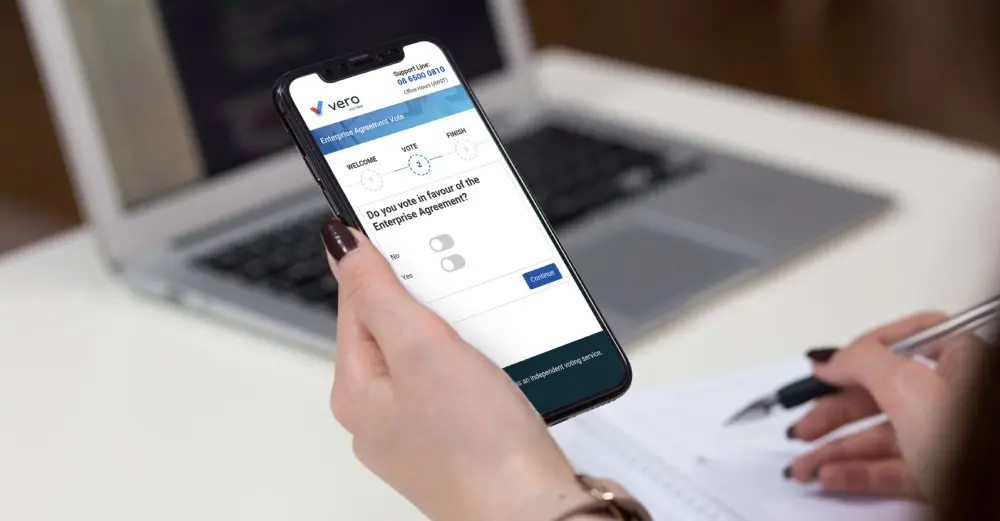
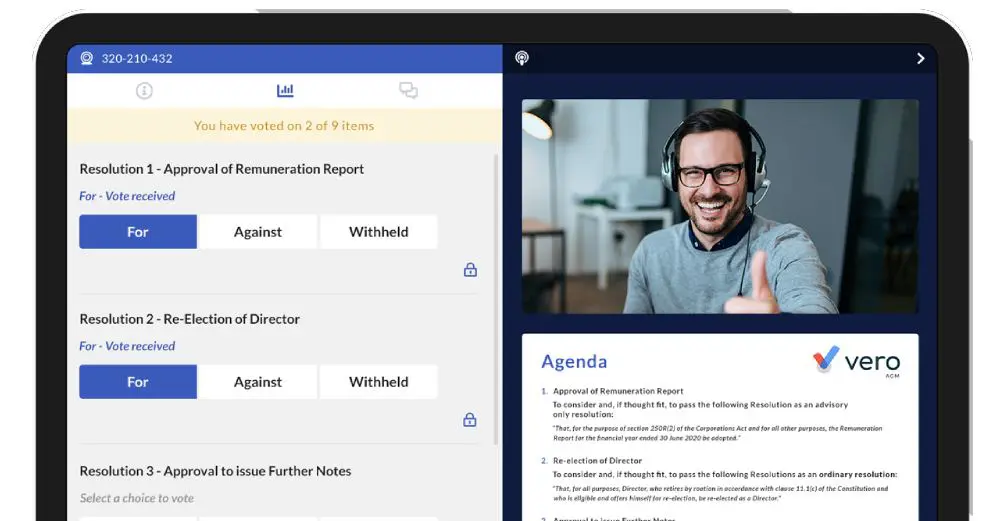
Vero Voting: Independently Verified Security You Can Trust
At Vero Voting, security is built into every stage of the voting process. Our platform is designed to align with Australian regulatory expectations while delivering a seamless, user-friendly experience.
We combine:
This ensures every vote is protected, every result is accurate, and every process is defensible.
Take the Next Step
If you are planning a ballot, election, or member vote, choosing a secure and compliant platform is essential. Vero Voting provides the expertise, technology, and independent assurance you need to run a trusted voting process.
Get in touch with our team today to learn how we can support your next vote—visit our contact page and start the conversation.